Sidebar
Add this page to your book
Remove this page from your book
Manage roles and users
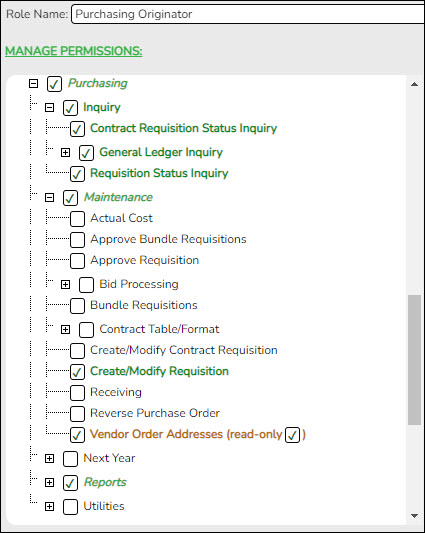
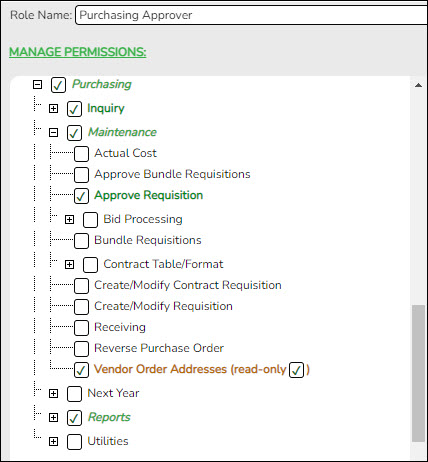
In Security Administration, set up the necessary purchasing roles (originators, approvers, etc.). Once the purchasing roles are established, assign the roles to the appropriate users. If a component (i.e., menu item) has a subcategory that is not selected, the upper-level title is displayed in italics. For example, if Utilities has sublevels, one of which has been cleared, then Utilities is displayed in italics denoting that not everything under Utilities is selected for permission.
To avoid any system issues related to roles, be sure to keep Business and Student roles separate and ensure that Business roles do not have campuses assigned.
You can generate the Security Administration > Reports > List of Users by Permission report to review user details such as the last login date and then modify as needed.
Security Administration > Manage Roles
Review the suggested minimum access for Purchasing originators and approvers.
Use the Security Administration > Manage Users page to assign the appropriate roles to the appropriate users.
Americans with Disabilities Act (ADA) and Web Accessibility
The Texas Computer Cooperative (TCC) is committed to making its websites accessible to all users. It is TCC policy to ensure that new and updated content complies with Web Content Accessibility Guidelines (WCAG) 2.0 Level AA. We welcome comments and suggestions to improve the accessibility of our websites. If the format of any material on our website interferes with your ability to access the information, use this form to leave a comment about the accessibility of our website.